This is a high-level visual participant taxonomy focused on individuals as cyber targets. It is a companion to my WordPress Blog post titled ” High-Level Visual Cyber Participant Taxonomy: Corporations as Cyber Targets”. Similar to the first corporate-focused cyber visual taxonomy, it is a pre-beta.
This visual taxonomy is meant to capture the participants who do or could help individuals before, during, and after they have been cyber-attacked. This pre-beta visual taxonomy, similar to the corporate one, has three categories – financial, services, and individual “retention”. I plan to add “government regulations” to the next version of this blog post.
Note #1: As with the visual corporate taxonomy, I have “buried” the panoply of brokers, MGAs, and others into the phrase “concomitant channels”.
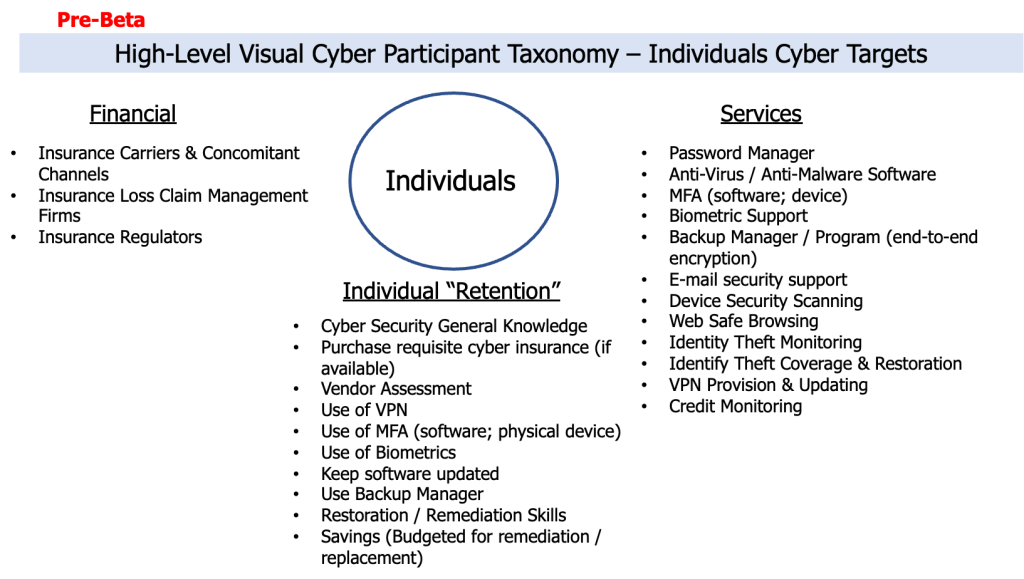
Note #2: The “Individual Retention” column encompasses the various initiatives which individuals should consider doing to minimize their being cyber-attacked at all (is that even possible?) or minimize the impact of being cyber-attacked.
I’m sure that I have left out “Services” that provide cyber security capabilities for individuals and / or initiatives in the “Individual Retention” column which individuals should be doing.
Please let me know what I have left out.
Consideration of the participants in this individual-focused cyber security visual taxonomy is equally as important as identifying the participants in the corporate-focused cyber security visual taxonomy.
The time has long past when corporations had the luxury of only securing their own operations and staff from cyber-attacks. The reality is that cyber-attacks can come from, at a minimum, “individual clients or prospects using unsecured devices or software” during the marketing, sales, and customer service processes; individual employees who bring their own “unsecured devices and software to work and connect to corporate devices or systems”, or individuals using “unsecured devices and software” to connect to devices or systems in any one or more of the participating firms in the various ecosystems the corporation uses to go-to-market and / or get-and-keep clients.