Each of us represents, at every moment in time, a totality of our life’s experiences, including education, relationships, and work experiences. A never-ending growing part of our life’s experiences include the impact that current and emerging technologies (and their associated applications) have on the manner in which we communicate; collaborate; consume entertainment and news; interact with prospects, clients and colleagues; travel; and perform other aspects of our daily lives.
All of the above (obviously) is true for insurance professionals, including (but not limited to): underwriters, product developers, marketers, actuaries, claim managers, and sales and distribution professionals. They, like each of us, bring their life experiences to bear when deciding whether and how to participate in the cyber risk market.
Four Dangerous Divides

I submit that insurance carrier professionals involved with the decisions of whether and how to participate in the cyber risk market, including the continual yes/no decisions of (initial and/or continual) participation and (continual) crafting of product terms and pricing decisions, should be aware how their life’s experiences could cause them to ignore four dangerous divides concerning cyber risk management:
- Insurance is primarily a social good vs insurance must be profitable
- Physical vs Digital Artifacts
- Nature of cyber risks (different in degree or different in kind)
- Focused vs Holistic approach to cyber risk management
Insurance: primarily a social good vs must primarily be profitable
After 4+ decades in the business side of the insurance industry (essentially encompassing all major lines of business except for health insurance and reinsurance), inclusive of 17 years within the industry, a decade of consulting to it, and over two decades as a technology-focused insurance industry analyst, I can’t believe the following even has to be stated:
The insurance industry is a profit-seeking industry.
I’ll double-down by stating that:
Just because a risk exists does not mean that insurance carriers must offer coverage for it.
Insurers offering coverage for a risk should only do so if, and only if, they can consistently do so profitably. That is, for P&C insurers, they should consistently offer cover if, and only if, they can generate combined ratios under 100%. Is that going to happen every year? Of course not. But that is the goal that insurers should be striving for each and every year they offer coverage for a risk.
Is insurance “a social good”? Yes, but! But only when insurers can consistently generate profit by covering the risk that is impacting society. Insurers need to predict their probable maximum loss for every line of business they provide coverage – and cyber coverage is no exception.
I’ll continue stating my argument that the insurance industry is a profit-seeking industry by referring to the dual responsibilities of insurance regulators: ensure the insurance client is treated fairly while simultaneously ensuring the financial viability of the insurance industry.
Regulators who focus on only one of those two responsibilities are doing a great disservice to both insurance clients and insurance carriers. Moreover, they are ignoring their reason for existing.
My (Obvious) Resolution: Insurance coverage must primarily be profitable.
Physical vs Digital Artifacts
Quite a few of us have been surrounded by, and use, physical artifacts throughout our lives. Physical Artifacts are those artifacts we can touch, feel, see, move (including seeing them move or tracking their motion), sometimes smell, sometimes hear, and sometimes bump into. Since the Information Era, people have come to realize that every physical artifact has some degree (or density) of data embedded in it. Of course, the artifact remains physical nevertheless. I think of those of us in this camp (and I am definitely a member) as digital immigrants.
Digital natives (people born after 1980), however, have had different life experiences. For them (and really, for all of us), physical artifacts are increasingly being displaced by Digital Artifacts (probably not as quickly as digital natives want). Digital artifacts can’t be touched, felt, seen, moved, smelled, heard, or bumped into as physical artifacts can be. Actually, they can be heard or moved or seen if we use IT / Telco applications to enable those results from digital artifacts.
When I think about or write about Digital natives, I always remember Alan Kay’s definition of technology: “Technology is anything that was invented after you were born.” And for the purposes of thinking about cyber, I propose we put the term ‘digital’ in front of ‘technology’ in Mr. Kay’s definition. (We need that particular focus because technology – and its various applications – has existed since humans first appeared on the planet. This historical fact brings up a rascally reality: not every technology is digital. )
But, physical artifacts are not going away: society is always going to have computing devices, communication devices, homes and home appliances, vehicles, corporate facilities, ground / air / ocean transportation, farms and farm implements, places of higher education, grocery stores, shopping centers (of some size), distribution centers, movie / streaming content sets, and terrestrial news media locations, at a minimum.
However, physical artifacts will become increasingly connected to the web and to each other – and to digital artifacts – using Internet Protocol (IP). [Obviously, we need IPv6 sooner than later as increasingly more IoT entities (Internet of Things … and animals … and people … and trees and plants) are becoming connected to the web.]
Different considerations providing insurance coverage: world of physical artifacts vs digital artifacts
When an insurance company decides to provide a mix of coverages to one or more physical artifacts, they have to take different (potential exposure and loss) considerations in mind than when they are providing a mix of coverages to a:
- physical artifact connected to a digital artifact
- digital artifact (e.g. an online publication is a portfolio of digital artifacts)
- digital artifact connected to the web (which itself is a digital artifact created and supported by physical artifacts)
Two hypotheses with dangerous implications
I’d hypothesize that insurance carrier professionals who have lived their lives (to this point in time) mostly surrounded by physical artifacts will tend to think that insurers can successfully cover cyber risk because it is just another risk that has emerged through the centuries for insurers to cover.
However, insurance carrier professionals who are digital natives will tend to think that technology (e.g. AI / Machine Learning, algorithms and predictive cyber loss models), and gathering enough data will provide the knowledge required to successfully cover cyber risks. (Success = persistent combined ratios under 100%.)
To me, it seems like hubris either way.
My Suggested Resolution: Insurance carrier professionals have to learn to operate (inclusive of target marketing, product development, pricing and reserving, offering customer service, and adjudicating claims) in a society that continues to have a mixture of physical artifacts and digital artifacts but is skewing quickly to encompass more digital artifacts and with more digital artifacts embedded within physical artifacts.
Nature of cyber risk (different in degree or different in kind?)
I state the following: Cyber risks are not different in degree from most other risks that insurers have encountered through the hundreds of years of the industry’s existence. Cyber risks are different in kind than in degree from previous risks, in multiple ways:
- Digital (specifically the digitization of data) is different in kind.
- Digital plus mobility is different in kind.
- Digital plus mobility plus connectivity (web) is different in kind.
- Digital plus mobility plus web plus IoT is different in kind.
Why?
A world continually shaped by cyber is significantly different (not in degree but in kind) than a world shaped (and populated) by physical artifacts. Three reasons:
- Each of the four above differences, but specifically 2, 3, and 4, continue to weave an ever-expanding hyper-dimensional digitally-driven society full of unpredictable emergent exposures (with unpredictable loss costs), including threads consisting of:
- digital to digital
- digital to ‘sensor-enabled physical artifacts” (e.g. IoT)
- ‘sensor-enabled physical artifacts’ to ‘sensor-enabled physical artifacts’ (e.g. IoT to IoT)
- digital to people (impacted secondarily by cyber attacks on digital systems)
- digital to IoT to people
- IoT to people.
- Data will not, and obviously can not, be available for newly emergent cyber risks that are different in kind from past or present cyber risks. No data from newly emergent cyber risks means no substantive models of newly emergent cyber risks means no substantive predicted cyber loss costs. (See my discussion of the dynamic of knowns and unknowns below.)
- The current and emergent world of cyber attack spaces and cyber risks are continuing to build a hyper-dimensional digital world that will adhere to three overarching principals.These three principals describe both natural and cyber-shaped business ecosystems:
- The ecosystem itself continues to change as various forces act on it (e.g. climate, introduction of new species in the natural world and Generative AI in the cyber-shaped business ecosystem world) and simultaneously within it (e.g. predator/prey interaction in the natural world and penetration / dynamic protection in the cyber-shaped business ecosystem world)
- Outcomes are unpredictable in terms of scale and scope (meaning, at least for me, predicting combined ratios for coverage for newly emergent cyber risks is algorithmic theatre at best)
- The rules of survival and adaptability change (for cyber targets and for cyber attackers) as the cyber-shaped business ecosystem changes.
The dynamic of knowns and unknowns
The three reasons above taken together, for me, means that identifying (previously unknown forms of) emergent cyber attacks and their concomitant losses (for insurance carriers who consider offering coverage) is an impossible objective to realize.
However, let’s delve into my opinion using the dynamic of knowns and unknowns.
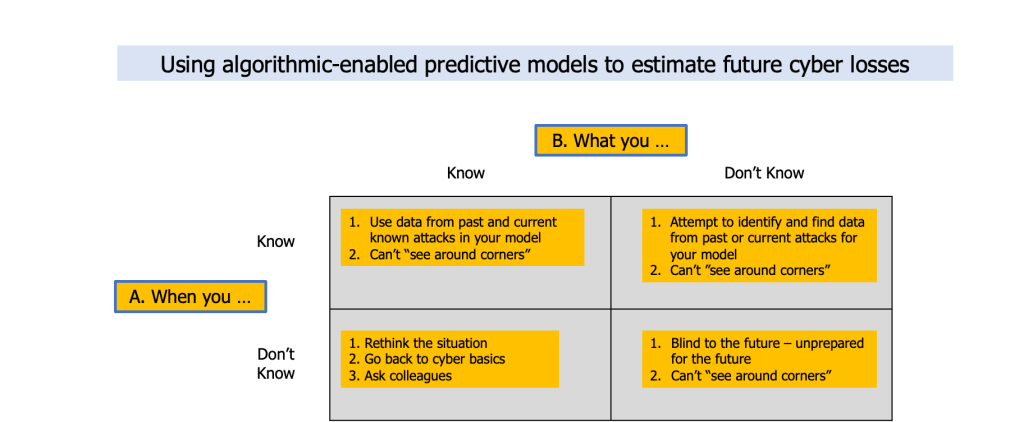
There are kernels of truth in this 2 X 2 and perhaps a tad bit of humor. I believe there are two kernels of truth concerning cyber risks in this 2 X 2:
- Nobody can see around corners to identify what is coming, particularly if it is a cyber risk that hasn’t appeared before; and
- Unknown unknowns (when you don’t know what you don’t know) will be the arena where a growing number of horrendous (uninsurable) cyber risks will emerge.
We’ll have to see what cyber risks (and their associated cyberinsurance losses) emerge in the months and years ahead to determine if I’m wrong or right.
My Resolution: Insurance carriers should realize that predictive cyber loss models which estimate loss information for newly emergent cyber attacks (over any future time period) whether for existing attack spaces or newly formed attack spaces are highly suspect.
Focused vs Holistic Approach to Cyber Risk Management
Both terms ‘focused’ and ‘holistic’ represent gradients of approaching cyber risk management in a focused manner or a holistic manner. The situation (of gradients) is similar to building a taxonomy which are, themselves, slippery to nail down.
As examples, a ‘focused’ approach includes a cyber risk underwriter considering the (known and potential digital) interactions of employees (whether geographically diverse or within one geographic location such as the headquarters) within one specific department of a company (e.g. sales, marketing, distribution of goods, storage). But a ‘focused’ approach could also include the considerations of every one of a company’s (known and potential digital) interactions with clients and/or prospects. A ‘focused’ approach might encompass the fusion of both of my examples.
A ‘holistic’ approach might include a company’s (known and potential digital interactions among and between participants of the) entire supply chain (with associated ecosystems of each participant in the supply chain). Or, a ‘holistic’ approach would augment my first ‘holistic’ example with known and potential IoT devices deployed throughout the company’s entire supply chain (and the associated ecosystems of each participant in the supply chain).
Or (last example), a ‘holistic’ approach might consider (the known and potential digital interactions of) one major industry – including its supply chains (and ecosystems of participants in it various supply chains).
Too few questions for either a focused or holistic approach to cyber risk management loss predictions
Do cyber attack / loss modeling firms create a “digital twin” or something similar of a company (or a specific department or an industry) to capture the various known – and potential – digital interactions among and between participants?
Do (re)insurers create a “digital twin” or something similar of a company (or a specific department or an industry) to capture the various known – and potential – digital interactions among and between participants?
Do CISOs and/or risk managers create a “digital twin” or something similar of a company (or a specific department or an industry) to capture the various known – and potential – digital interactions among and between participants … and use the cyber loss models to determine the best ways to continually secure their companies?
My Resolution: I don’t have any “you should do this” suggestions for (re)insurers deciding to create cyber loss prediction models. I’d want to use a “digital twin” of all known and potential digital interactions among and between participants of whatever scale (one department, two or more departments, the entire company, a supply chain, an industry) a (re)insurer decides to base the cyber loss prediction models. Regarding the purchase of cyber risk loss prediction models, I’d want to know the specifics of what elements went into the model, what assumptions were made, and what data was used (and from which inputs) – I’d also want to know how often the model (and data inputs and assumptions) is updated.
Summary
Each of the four divides – specifically the first three – is dangerous, whether separately or in any combination, because depending on which side of the divide an insurance professional focuses on (or believes is true) can lead to unprofitable cyber insurance business results.
The fourth divide can also be dangerous if the “correct” perspective (focused or holistic) is not used for whatever the situation is that the (re)insurer is considering offering cyber insurance.
I continue to believe that cyber risks are inherently uninsurable … but perhaps (re)insurers knowing how best to bridge the “dangerous divides” to generate profitable business will buy some time. Hopefully the (re)insurers will not also be “buying horrendous combined ratios” during that time.