The insurance industry is shifting from one portfolio of risk events that it has identified and managed profitably for thousands of years to a new, and significantly different portfolio of risk events: a plethora of cyber risk events that the insurance industry erroneously believes it can successfully identify and manage profitably.
Specifically, the insurance industry has historically conducted commerce where the existence of risk events occur from interactions between and among people and (too?) often times between and among people and physical artifacts, digital artifacts, and / or nature.
In the Cyber Age that society is quickly shifting into, the insurance industry is facing a new – and rapidly expanding – portfolio of risk events emerging from interactions between and among people and cyber age artifacts and increasingly between and among the coupling of people and cyber age artifacts and some combination of digital artifacts, physical artifacts, and / or nature.
Moreover, the new world of cyber risks (e.g., that world is the Cyber Medium) is in the process of layering itself on, and extending itself over, the traditional world of risks.
Plainly stated, insurers are facing two worlds of risks – traditional and cyber – to compete successfully. However, having experience of financially succeeding in the traditional world is not sufficient to financially succeed in the cyber world.
My point-of-view, based on research and discussions that began in January 2023, is that the insurance industry should not be facing the cyber risks of the Cyber Age in the first place. Similar to risks from Terrorism (and risks of business interruption during a global pandemic) cyber risks are not insurable. I’ve written several WordPress blog posts discussing my rationale (and I will put them or similar reasoning in my forthcoming book about the insurance industry and cyber.)
I realize from discussions, articles, video interviews which I have watched, and LI threads, that many (almost all?) insurers are, and have been, generating combined ratios that are under 100% from their cyber insurance book of business. (Does that refer to sales of insurance lines of business where cyber insurance is included (silent cyber) or sales of only cyber insurance?).
However, I don’t believe that profitable results from the sales of cyber insurance will last (whether stand-alone or silent) because:
- Cyber risks will become more complex over the weeks and months ahead;
- Cyber hackers will increasingly target industries and enterprises:
- not able to protect themselves
- providing a critical service to society
- not able to become resilient as quickly as they should (whether from a societal perspective or from an ability to begin conducting commerce quickly);
- Cyber tail losses will become both more unreasonable and more apparent as the cyber insurance book of business reveals increasingly more systemic cyber attacks and concomitant losses.
Explaining the shift to the Cyber Age
I’m using this blog post to discuss the shift to the Cyber Age, why cyber risks are not just different but other-worldly different than traditional risks, and a new concept (from my previous cyber-related discussions) of the Cyber Medium. I’m going to lean on Marshall McLuhan to help me discuss why cyber risks are unlike ‘traditional’ risks and live (and grow and expand) in the emerging Cyber Medium.
Let’s consider the creation of the Cyber Age first.
The Creation of the Cyber Age
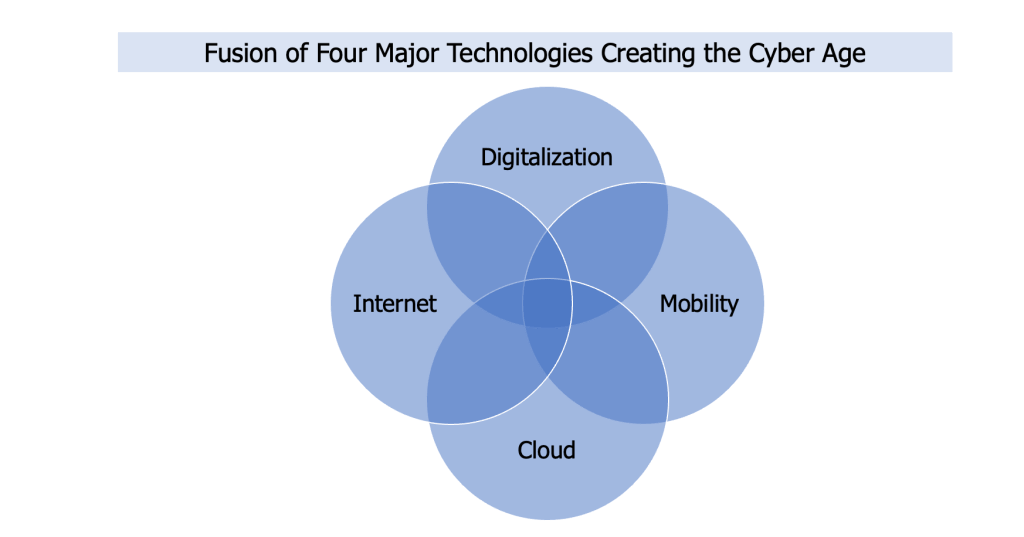
There are four major technologies – and their associated applications – which have been fusing, and continue to fuse, together to create the Cyber Age.
Those four technologies are (not shown in time order of discovery or general implementation):
- Digitalization
- Mobility
- Cloud
- Internet
Note: The use of AI technology applications did not create the Cyber Age. However, when AI technology applications (any of which generate a probabilistic outcome) are used in conjunction with the below four technologies (each of which is a deterministic technology), the result is a probabilistic outcome (e.g. a result that ‘hallucinates’, drifts, is a mistake, is wrong). When AI technology applications are used, it is not so much a matter of “trust” but a matter of “tolerance” (e.g. how large a gap can the user tolerate between the given result and the expected result?)
A technologist might say that the existence of the Cyber Age was inevitable given the advancements in information technology and telecommunications technology since the Agrarian Age. Regardless of its starting point, or points of origin, increasingly more of society is living in the Cyber Age.
The Cyber Age encompasses any and every web-enabled, cloud-accessible, mobile, digital societal interaction desired to be accomplished through the support of the four technologies and their growing set of applications. The four technologies and their applications are not just establishing – and growing – the Cyber Age, but they are also forming “the Cyber Medium” (I discuss the Cyber Medium below in the section labeled “The emerging Cyber Medium”.)
The nature of the shift to the Cyber Age
However, before discussing the emerging cyber medium, I want to discuss the nature of the shift to the Cyber Age.
I don’t see the nature of this shift as a smooth shift from the past or as a many-step shift from either the present or the past.
The ‘smooth’ or ‘many-step’ shift mindset would be way too “business-as-usual” for my thinking. It would imply, or worse, give license to insurance professionals to believe that how the insurance industry thought about, identified, and decided to offer (or reject) insurance coverage throughout the thousands of years the insurance industry has existed is the same or similar to how insurers should think about, identify, and decide to offer (or reject) insurance coverage for risks in our current and expanding Cyber Age.
I certainly don’t intend for any person – whether a professional in any part of the insurance industry or a client of any enterprise facing cyber risks – to believe that any risk in the Cyber Age is “just another risk which insurers have managed in their vast existence of time” or “all insurers need is more data” or “all insurers need is more of the ‘right’ data” to create accurate cyber risk loss models as input to the decision to offer (or not offer) coverage for one or more cyber risks.
That is not my intention.
For my part, and as I have written, I believe that cyber risks are nothing like any risk which the insurance industry has seen and provided coverage for in its thousands of years of existence.
The essence of the risks which the insurance industry has managed throughout the centuries have been, and are, as I alluded to above, some combination of one or more exposures to people; people’s property (e.g., homes, vehicles, enterprises, business facilities, etc), financial assets, behaviors, and/or actions; and/or the physical assets of the enterprises they owned, managed, or worked for; and/or the actions and/or behaviors of the owners, executives, or employees of enterprises; and/or the behaviors of the natural environment.
These ‘traditional’ risks are not disappearing although some might be headed to the history bins at some point in the future.
Turning to the Cyber Medium
I want to repeat that ‘traditional’ risks will exist in society at the same time that cyber risks are evolving and becoming more complex in the expanding Cyber Medium of the Cyber Age. Insurers deciding to continue to offer coverage for cyber risks should have an understanding of the Cyber Medium.
First, I strongly believe that the emergent expanding plethora of other-worldly Cyber Age risks is itself a message of the Cyber Medium.
Beyond that belief, there are three questions I want to discuss regarding the Cyber Medium:
- What are the three forces shaping the emerging Cyber Medium?
- What are some Cyber Age artifacts in the Cyber Medium
- Why are cyber risks (from the Cyber Medium) different than ‘traditional’ risks?
The emerging Cyber Medium
I want to mention the two topics again: Cyber Age and Cyber Medium to emphasize that the Cyber Age and the Cyber Medium are not equivalent. The latter is a part of the former. There is more to the Cyber Age than the Cyber Medium. However, for the purposes of this post I will focus on the emerging Cyber Medium.
The Cyber Medium is becoming an immersive environment in which society will increasingly conduct commerce, communication, collaboration, and consume (or create) entertainment and news. Currently, this immersive environment is primarily passive from a consumer or end-user perspective but with advances in voice recognition, VR , AR and other technology applications, it will become increasingly interactive.
(Note: Whether passive or interactive, the relationships within the Cyber Medium [among and between the coupling of people and Cyber Age artifacts as well as among and between that coupling and digital artifacts, physical artifacts, and nature serve as a infinite set of pathways for current and future systemic cyber attacks.)
But how is the Cyber Medium becoming a critical component of the Cyber Age?
Marshall McLuhan and the three forces shaping the Cyber Medium
There are three forces continuously shaping the Cyber Medium. Interestedly enough for me, I discovered that Marshall McLuhan discussed them in one of his books: “Understanding Media: The Extensions of Man” Mentor, Published by the Penguin Group, 1964. In it, he stated:
“For the “message” of any medium or technology is the change of scale or pace or pattern that it introduces into human affairs.” (I was always taken with his confluence or equivalence of ‘medium’ and ‘technology’
Obviously, I’m playing off of Marshall McLuhan’s statement that “The Medium is the Message” in the title of this WordPress blog post by inserting the word “Cyber” in front of the word “Medium”. I did that because Marshall McLuhan’s points-of-view about media – and technology – speak to the realities of our current and expanding Cyber Age.
It is the changes of scale, pace, or pattern among and between the coupling of people and cyber age artifacts as well as among and between the coupling of people and cyber artifacts and digital artifacts, physical artifacts, and/or nature that is redefining the nature of all of society’s interactions in the Cyber Age and creating an otherworldly plethora of (cyber) risks.
One visualization of the Cyber Medium might look like something out of the Matrix movies:
Source: Search for wall of 1’s and 0’s on Bing.com – to represent the medium of the Cyber Age
You can also think of the above visual as a very simplified view of the Cyber Attack Space topography. The flow of ‘1’s and ‘0’s represent the interconnection among and between the coupling of people and cyber age artifacts and digital artifacts, physical artifacts, and nature.
The Cyber Attack Space topography has: No buildings, no landscapes, no cityscapes, no seascapes, no mountain-scapes, no vehicles, no homes, no facilities, no people, no entertainment venues, no shopping malls, no highways, no streets, no roads, no vehicles (consumer or corporate), no airplanes, no ships (commercial or otherwise), no physical artifacts at all, no picturesque visions of nature, no people, not animals (including farm animals), no insects … just a flow of ‘1’s and ‘0’s. Unless the physical artifacts or sentient beings I listed have IP sensors embedded in them or on them.
What are some Cyber Age artifacts in the Cyber Medium?
Humans as a species are a social, love to communicate (well, not everyone ‘loves’ to communicate), and build, use, and share artifacts. For many thousands of years, the artifacts have been physical artifacts (e.g., tangible artifacts such as farm tools and equipment, transportation vehicles, buildings, homes, typewriters, telephones, telephone poles, …) and relatively recently (on a anthropologic scale) the artifacts have been digital artifacts (e.g., intangible artifacts such as data, processes, software solutions, telephone calls, images, video, captured sounds, …).
I don’t think it is a stretch to state that every Age that humans have lived in have one, two, or possibly three artifacts (whether physical or digital) that are iconic artifacts of that particular Age.
Now, as society progresses into the Cyber Age, humans are building, using, and sharing Cyber Age artifacts. Honestly, I believe we’re more in the Cyber Age artifacts ‘building’ phase currently
My current description of a Cyber Age artifact is (preferably all four of these attributes):
- a tangible or intangible entity connected to the Internet (or web) at a minimum;
- digital, mobile, and deployed in one or more types of cloud (private, public, hybrid);
- human, animal, tangible object, software process, firmware (e.g., encompassing both hardware, software, and telco capabilities);
- capable of sending or receiving data (about its status and/or changing and/or activating its capabilities).
One way to bring these four attributes together is that a Cyber Age artifact is not just connected, but interconnected.
Moreover, with an enterprise that is conducting commerce in the Cyber Age, the enterprise will have a portfolio of interconnected and interdependent Cyber Age artifacts both within the enterprise and between the enterprise and the various other firms and people (e.g., sales, distributors, outside law firms, regulators, clients, prospective clients) that it depends on or ‘touches’ during the course of its operations.
My description of a Cyber Age artifact may change by the time I’m finished writing my book. I’m open to hearing your thoughts about how you would describe a Cyber Age artifact.
Why are (cyber) risks different than ‘traditional’ risks?
Now, we’ve arrived at a point in the blog post which many of you have been waiting for – what’s so ‘other-worldly’ about cyber risks? Why are risks that emerge in the Cyber Medium so different than the risks which the insurance industry has identified and successfully underwritten for thousands of years?
I have already provided part of the answer at the near the top of this post: In the Cyber Age that society is quickly shifting into, the insurance industry is facing a new – and rapidly expanding – portfolio of risk events emerging from interactions between and among people and cyber age artifacts and increasingly between and among the coupling of people and cyber age artifacts and some combination of digital artifacts, physical artifacts, and / or nature.
Let’s go deeper and augment the above paragraph with a consideration of the four technologies and their applications that created the Cyber Age and the three forces that form the Cyber Medium: changes of scale, pace, or pattern among and between every type of societal interaction.
Cyber risks are ‘other-worldly’ because they:
- Can and do happen simultaneously across what might be considered separate ‘targets’ (but in reality are connected) in a spatial context. The context may be enterprises (inter)connected with firms in their ecosystems and/or suppliers and/or clients conducting commerce with them. A cyber attack may target one specific business operating system of an enterprise (whether bank or hospital or Las Vegas casino or a healthcare payment services firm) but there is a high probability that the attack will also simultaneously impact clients, patients, consumers, or other enterprises);
- Can not be underwritten as separate, disconnected, apart, fragmented, spatially alone, spatially distant, or silo-ed from other activities or processes or business divisions or third-party contractors or partnerships or alliances or clients or sales or distributors of the cyber-attacked enterprise;
- Demand that insurers take a holistic perspective augmented with a realization of simultaneity happening with every interconnection a cyber attacked enterprise / organization has established.
I hypothesize that if insurance underwriters ignore the reality of cyber risks, the resulting tail losses will be rather unpleasant.
Finishing Up: Insuring two very different worlds of risk
The insurance industry is facing two very different worlds of risk: traditional risks and cyber risks. There are several challenges for insurers who insist on putting their financial capacity at risk in the Cyber Age, specifically covering cyber risks that exist and continue to emerge in the various cyber attack spaces within the Cyber Medium.
The biggest challenge to overcome is thinking that cyber risks are “just another risk” that the industry has faced through the centuries of its existence. The second biggest challenge to overcome is that thinking that “all we need is to collect more data or more of the “right” data”and we can then successfully underwrite cyber risks. I’ve discussed why this second challenge can’t be overcome in previous blog posts but I’ll reiterate my point, every instance that a:
- digital artifact is connected to the web, the cyber attack space unfolds in multiple dimensions and multiple directions;
- physical artifact with embedded telco capabilities is connected to the web, the cyber attack space unfolds in multiple dimensions and multiple directions;
- digital artifact is connected to a telco-embedded physical artifact that either one of them is already connected to the web, the cyber attack space unfolds in multiple dimensions and multiple directions.
Another challenge that insurers face is monitoring when one or more of their client’s traditional risks becomes a cyber risk. For example, when a ‘traditional’ home appliance, automobile, or manufacturing plant connects an activity or a process or a physical artifact (e.g., cog, valve, wheel, …) to the web, it becomes a Cyber Artifact. If that entity then becomes mobile-enabled and/or is deployed in the cloud, it becomes more of a Cyber Artifact.
I have a hunch that the lines of business policies which the insurer initially sold the customer or the manufacturer (or the warehouse owner) or … that insurance policies are no longer fit-for-purpose and need to be rewritten or withdrawn or non-renewed.
Insurers need to continually monitor and measure the combined ratio of their total book of business, their cyber book of business for the silent cyber policies on their books, and their ‘pure-play’ cyber policies on their books.